Eliminating Infectious GEFEST Ransomware Virus From Your System
The irony of this menace GEFEST Ransomware is that it encrypts data & avowedly obliges money as a bribe to get it altered. It encrypts files by installing the GEFEST extension; it will then transmit ransomware preparations as a desktop wallpaper icon.
It also holds on scanning the substance and intimations constantly that how you could seek conceivably to recover some of your fastened files & data.
GEFEST Ransomware is a dangerous peril malware virus incorporated with robust encryption algorithms used for encrypting, though it completely encrypts your files & data that you will not be capable to obtain them for long spun.
Furthermore, it leaves the bribe image on your screen asserting how to obtain encrypted files & data. It conveys erudition concerning the method to get the decryption key to unfasten your data.

It summons users to communicate hackers via emails to get decryption key & unhitch your data.
These phishing emails look like reliable advice from customary organizations or co-operation. The virus cryptogram might be rooted in scripts direct ascribed to the emails.
The GEFEST Ransomware infectious file purportedly redirects to ill-disposed websites that pretend as harmless as download portals & landing pages.
These enclosed codes can be fixed in multiple payloads; this significant virus code can be installed in the most common document types:
The cyberpunk can set up data of accessible software that is frequently downloaded by utmost users:
The GEFEST Ransomware as a newbie born of this malware strain & can be managed to carry out an expanded list of operations depending upon the contour file issued by the hackers.
Read More :- Click here
It also holds on scanning the substance and intimations constantly that how you could seek conceivably to recover some of your fastened files & data.
GEFEST Ransomware is a dangerous peril malware virus incorporated with robust encryption algorithms used for encrypting, though it completely encrypts your files & data that you will not be capable to obtain them for long spun.
Furthermore, it leaves the bribe image on your screen asserting how to obtain encrypted files & data. It conveys erudition concerning the method to get the decryption key to unfasten your data.

It summons users to communicate hackers via emails to get decryption key & unhitch your data.
GEFEST Ransomware Distribution procedure:
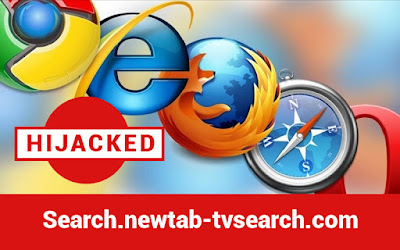
The inception process used by GEFEST Ransomware variant is via coordination of Phishing messages that are designed by using escapade tools to transfer out bulk amounts of emails & messages.These phishing emails look like reliable advice from customary organizations or co-operation. The virus cryptogram might be rooted in scripts direct ascribed to the emails.
The GEFEST Ransomware infectious file purportedly redirects to ill-disposed websites that pretend as harmless as download portals & landing pages.
These enclosed codes can be fixed in multiple payloads; this significant virus code can be installed in the most common document types:
- Presentations
- Databases
- Text documents & spreadsheets
The cyberpunk can set up data of accessible software that is frequently downloaded by utmost users:
- Office & productivity tools
- System utilities
- Creativity suites
The GEFEST Ransomware as a newbie born of this malware strain & can be managed to carry out an expanded list of operations depending upon the contour file issued by the hackers.
- Boot Modifications: The GEFEST Ransomware can establish itself in a form that transforms the core boot settings, as a result, this virus will begin itself robotically once the system powers on.
- Retrieval information: The Virus can investigate the system for sensitive erudition about the identification of the quarry users & machine metrics.
- Security Service: Examples of protection services and applications that the virus turbine can look for intersection & also permit it to quietly install itself on the victim computers.
- Windows Registry: Hazardous effects of ransomware contagions, that the alteration of the registry of the arbitrated machines, it also performs the system completely unusable and works in unfamiliar ways.
- Payload delivery: GEFEST ransomware variants of this type choose to deploy other threats as well. This Ransomware has already bypassed the security barriers.
Read More :- Click here

Comments
Post a Comment