How to get rid of Malicious Turla Trojan?
Guide to Remove Turla Trojan
Turla, also known as Snake or Uroboros, is a malicious Trojan that has been targeting systems of government and military’s interest since year 2008. Turla Trojan is suspected to be originated by hackers from Russia.
Turla Trojan Virus has infected innumerable systems in around 45 countries like Iran, Kazakhstan, USA, Russia and China, with France ranking on the top of the hit list. The targets of Turla Trojan Virus include government entities like Ministry of Trade and Commerce, Ministry of Foreign/External affairs, intelligence agencies, embassies and educational firms. The attackers are focused on gathering the information about a country’s economy by deploying phishing e-mails smartly in targeted systems.
Threat Behavior:
Threat Behavior:
Kaspersky, Symantec and The Laboratory of Cryptography & System Security conducted an analysis in Budapest, Hungary on the working methodology of Turla Trojan. The analysis revealed that the operators that drive Turla Trojan Attack are using highly sophisticated techniques. Turla Trojan is a collection of these sophisticated backdoors and malware that is led by the hackers.
Backdoor is a methodology of securing the system by obtaining its encrypted information in plain text. The attackers use Trojan.wibpot and Tavdig as a backdoor to collect the victim’s system information and to gain unauthorized access to system resources. The information may include IP address, browsing history and details of applications installed in the system.
They carry out this cyber espionage by sending phishing e-mails and watering hole-attacks to the potential victims. Watering holes include the websites that are frequently visited by the victim. These websites redirect the victims to Java or browser exploits (corrupted web pages) through which vital information (like login credentials, passwords) can be decrypted and used by the attackers!

Once a system is infected, the main module of pre-configured batch files is delivered which automatically triggers launch of commands for execution. Some of the actions that the attackers can launch/execute on an infected system are:
- Delete File: Imagine losing an important photograph without you deleting it! Hackers may delete any number & type of files from your computer!
- Get File: A serious threat to your privacy, your system traces can be picked by these attackers to retrieve your browsing interests and then spam your inbox by sending annoying e-mails related to your browsing.
- Run Shell Command: Imagine a single remote command by the hacker could crash your system at any time!
- Sleep: Imagine your system triggers to sleep mode in the midst of an important banking transaction
Spread Techniques:
The cybercriminals use various strategies for malware distribution which include –
- Software Bundling: Software bundling is the process in which a malicious program is distributed with other free software, to get an unnoticed entry into your computer system. When a user installs a free application, the malicious programs gains a front door entry with the free application, the user has downloaded. Thus, it is a good idea to keep an eye on the installation screens while installing these free applications.
- Infected Storage Devices: Your system can also get infected by using removable media such as USB hard drives and jump drives without scanning them with an anti-virus.
- Spam Emails – Spamming is the most economic and common method used for the distribution of such malware. The targeted users get genuine looking emails which contain .doc, .txt, and other similar attachments. These attachments can be named as anything which can grab the user’s attention and triggers him/her to open the attachment. As soon as the user opens this attachment, the malware infects the user’s computer system.
- Malicious Websites or Malevolent Advertisements: The malicious websites are the ones which are created just for promoting the malware infections. Such websites include but are not limited to porn sites, torrent sites and other free downloading platforms. By visiting such websites, the adware infects the user’s computer without permission. Fake advertisements and updates like Flash player and windows updates which ask the user to update to the latest version are a few examples. When the users click on such links, their computer system gets infected. That is why, it is highly recommended to resist clicking on such links. Also avoid clicking on advertisements offering free stuff such as Win an iPhones, cars or free overseas trips etc.
Threat Summary:
Name: Turla Trojan
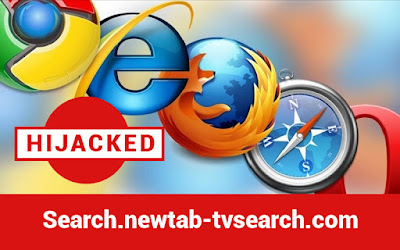
Browsers Affected: Google Chrome, Mozilla Firefox and Internet Explorer etc
Targeted Operating System: Windows, MAC, Android, Iphone
Category: Trojan
Symptoms: Appearance of annoying ads, popping up windows and changing desktops, Installer Bundles, deletion of files automatically, creation of new directory or folders, spam e-mails/messages that may redirect the user to another webpage and interrupt their browsing activity.

Read Full Article :- Click here

Comments
Post a Comment